Blog
FortiCloud SSO Vulnerability and Best Practices
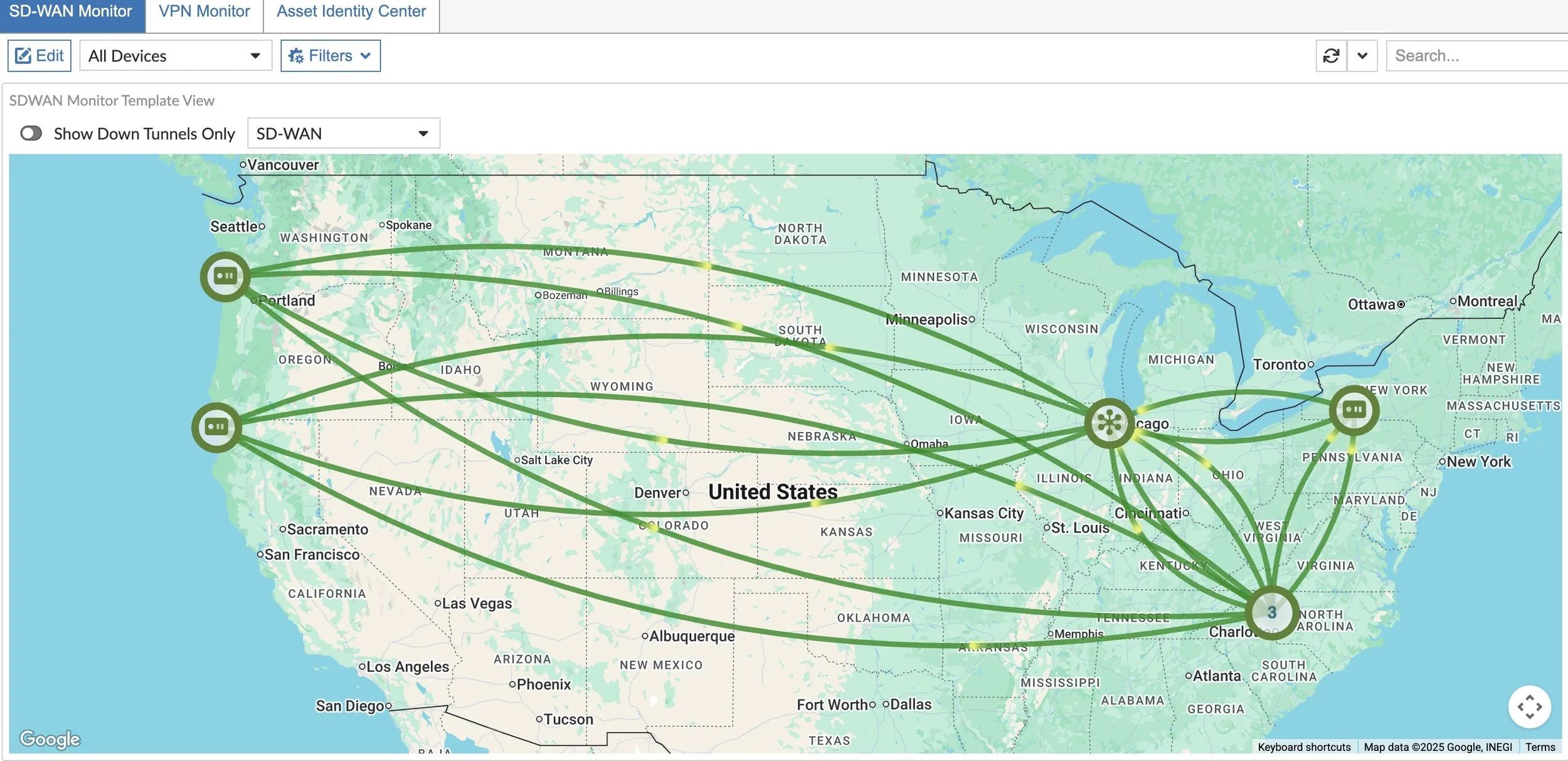
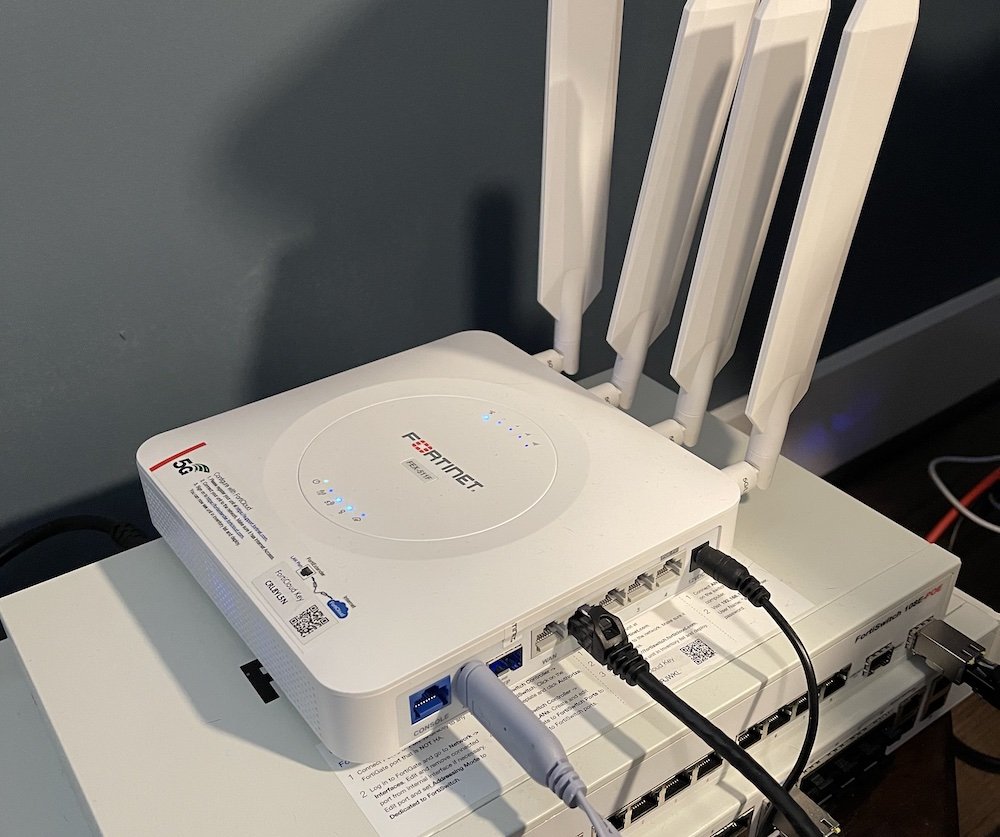
SD-WAN Lab in FortiManager 7.6
With a fresh ProxMox installation and new FortiManager 7.6 deployment, join me as I rebuild my SD-WAN lab to use for customer demos and proof of concepts!
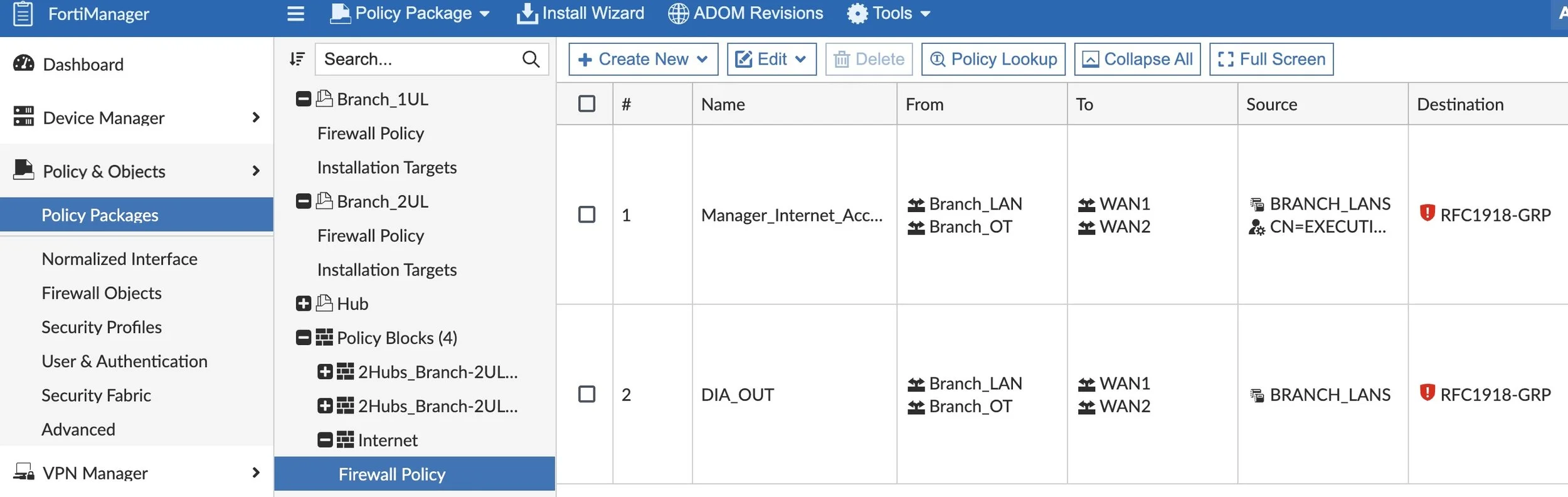
Sequence Groupings vs. Policy Blocks
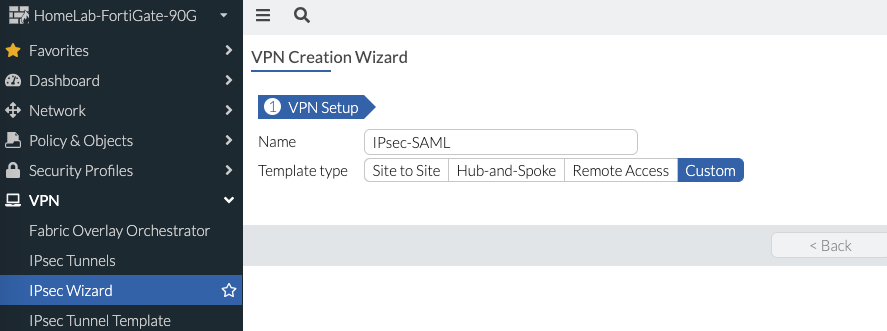
FortiGate IPsec VPN with SAML
I stumbled upon a heated and spirited debate: SSL VPN vs. IPsec VPN for remote access. As you know IPsec VPN predates SSL VPN, but was eventually replaced with SSL VPN due to the ease of deployment where some networks blocked IPsec traffic mixed with the inconvenience of distributing the IPsec preshared key with the VPN client. Fast forward to the present and SSL VPN is one of the most commonly attacked and exploited implementations. Just search for CVEs targeting Fortinet, Palo Alto Networks, Cisco, Checkpoint, F5, SonicWall, Ivanti, etc. and you’ll find plenty regardless of vendor. Why? Remote access is an incredibly effective method for attackers to gain access to a target’s network. And not to mention brute force and password spraying attacks targeting SSL VPN…
I won’t argue which VPN solution is more secure — both have their pros and cons. But what if you wanted to implement IPsec VPN and still leverage SAML for multi-factor authentication? Fortinet has documentation on how to implement this, but I wanted to document how I set it up since it took me a few attempts with some lessons-learned. Read on!

FortiGate SSL-VPN Hardening

FortiGate Admin SSO with SAML

Using FortiFlex to License FortiGates
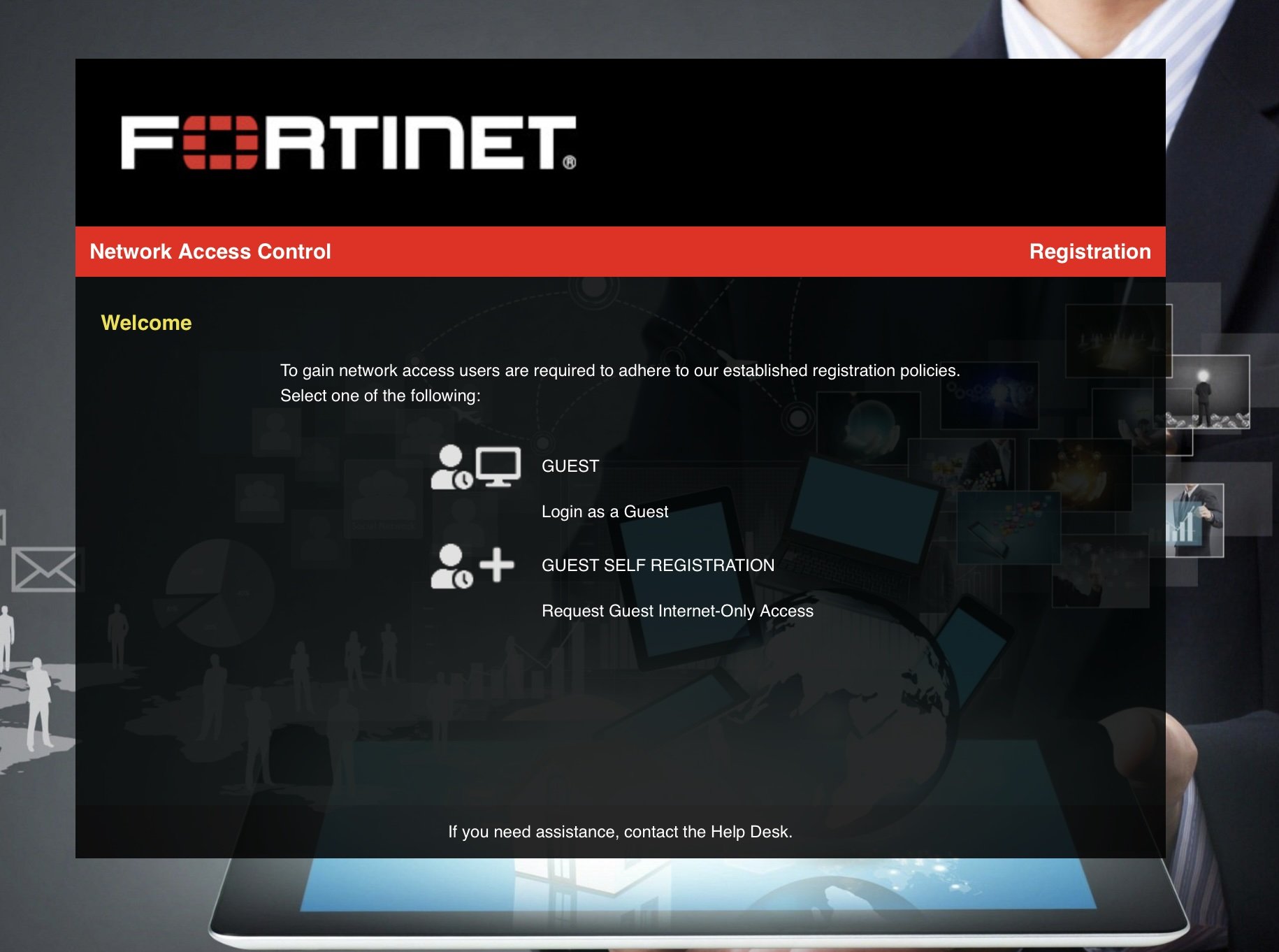
FortiNAC for Guest Access Using a Captive Portal

Fortinet Zero Trust Network Access (with SAML)